An updated 2015 analysis of password reset examples from Troy Hunt: Everything you ever wanted to know about building a secure password reset feature (May 22, 2012) performed April 16 & 17, 2015
I was reading through the post and wondered in nearly three years what, if anything, has changed with the examples provided?
Short answer: largely nothing security-wise
US Outdoor changes:
- Slight theme update
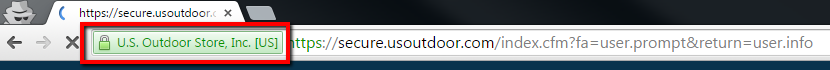
- Extended Validation SSL certificate
- Uses HTTPS for logon page (issues there also)
2012

Clearly the first problem is that the logon page hasn’t been loaded over HTTPS, but then they’ve also gone and offered to “Send Password”. Now maybe that’s an example of the earlier mentioned colloquial use of the term, let’s dig a big further and see what happens:
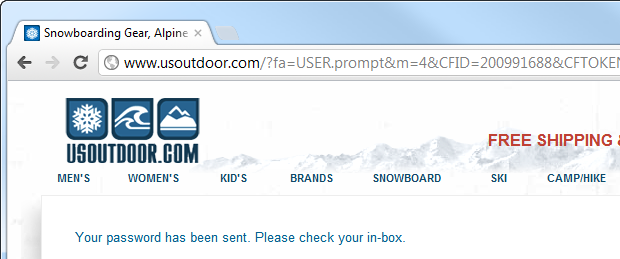
2015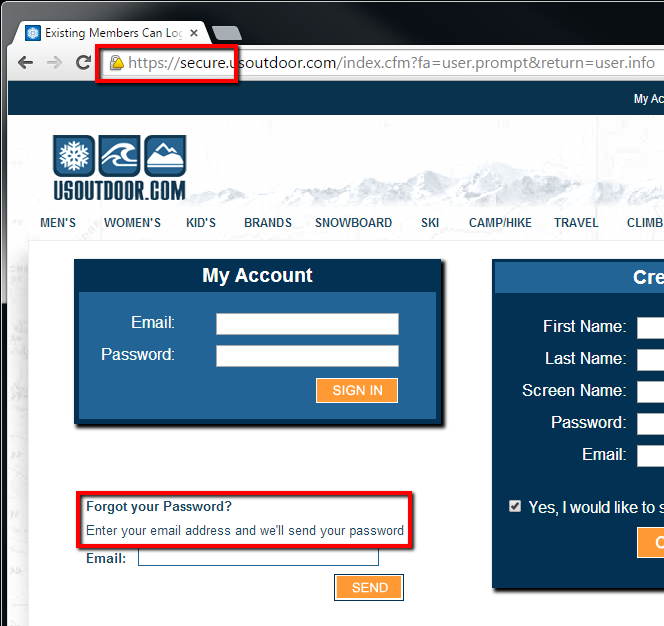
- You will notice the logon page now loads over HTTPS, but there is a mixed content warning (see below).
- The text “Enter your email address and we’ll send your password” clarifies that yes, they will be sending your password and not a reset link.
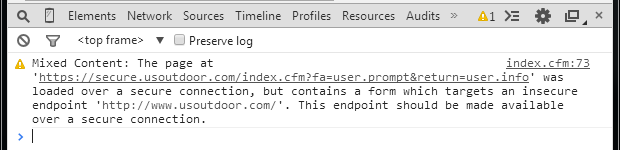
Looks like it is the search form in the header:
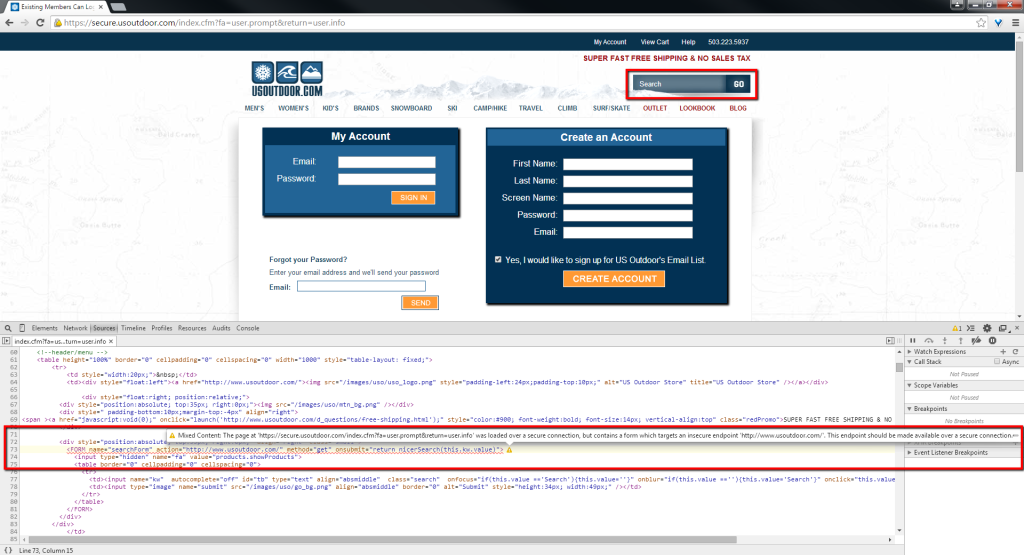
They incurred the extra expense of a extended validation SSL certificate, you’d think they’d want it to display correctly on all pages.
Back to the original analysis…
2012
Not looking much better, unfortunately and the email confirms the problem:
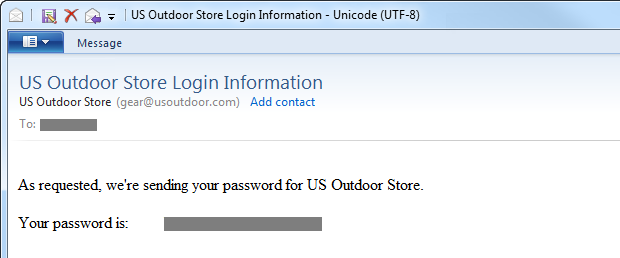
2015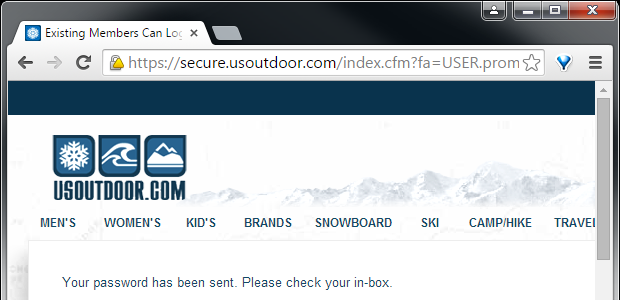
Exactly the same.
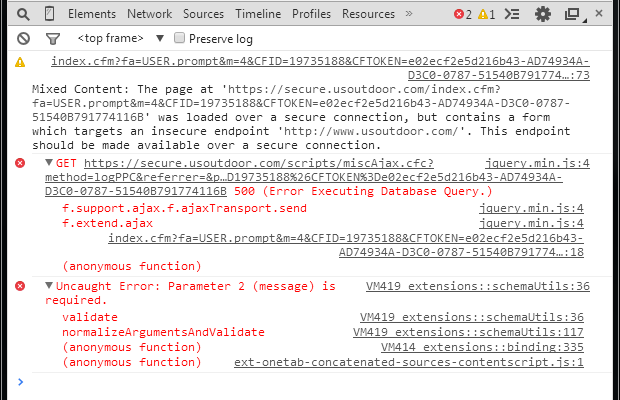
Wait, there are 2 errors and 1 warning (the same mixed content warning as before) in the console…
and the email…
2012
So this tells us a couple of important things about usoutdoor.com:
- They’re not hashing the password. At best they’re encrypting it but they’re quite possibly just storing it in the clear; we have no evidence to the contrary.
- They’re sending a persistent password – one we can go back and keep using over and over – via an insecure channel.
2015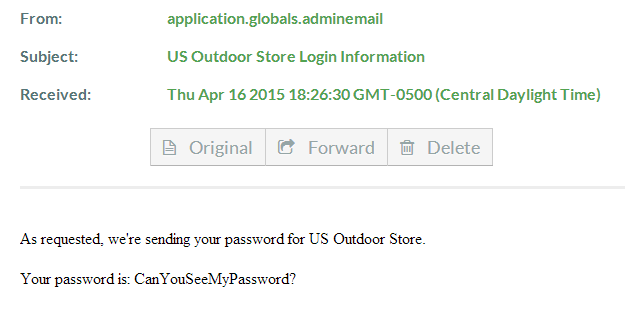
Clearly you can. Again, exactly the same.
Still no evidence whether the password is encrypted or stored in the clear, but it obviously isn’t being hashed.
Don’t worry, I changed the password after this analysis, which brought up a completely different set of usability issues I plan to detail later. Basically it boils down to disallowing characters and truncating passwords without warning. It was easy to discover the latter however, because they just email my password back upon request.
Original analysis and images courtesy of Troy Hunt licensed under a Creative Commons Attribution 3.0 Unported License.
Work on this page is also licensed under a Creative Commons Attribution 3.0 Unported License.